How Nidhi Razdan Could’ve Saved Herself from the Phishing Attacks
SendX
JANUARY 17, 2021
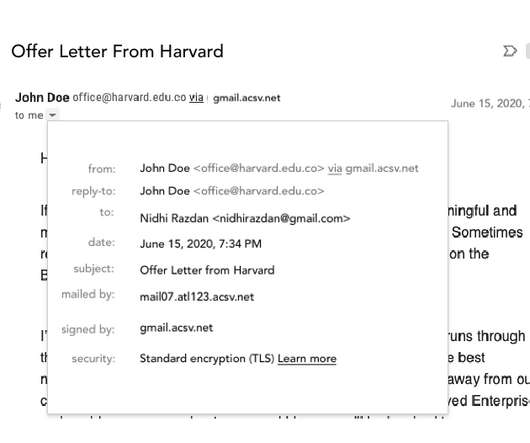
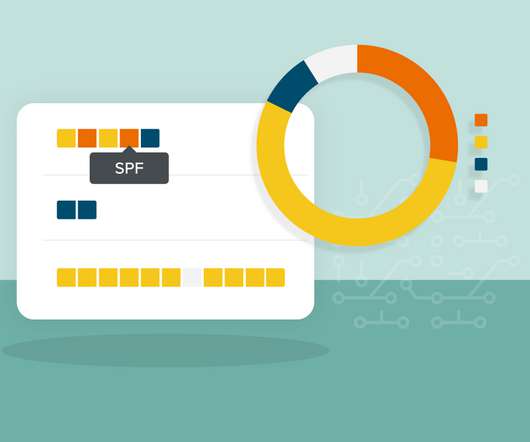
The recent case of a phishing attack on Nidhi Razdan is an eye-opener! She recently disclosed on Twitter that she has been a victim of a sophisticated phishing attack. With the benefit of hindsight that we all have now, let's educate ourselves on how to not be a victim of phishing attacks. What is phishing?







































Let's personalize your content