How bad data can spoil good personalization
Martech
AUGUST 31, 2022
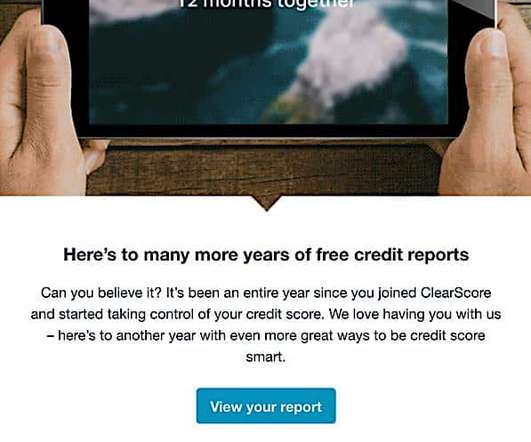
But each email had a personalization failure that shows this transition from promotional to customer-focused email marketing still has a long way to go. The copy in this reminder email is spot-on for brand voice and helpful information — warm, personable and persuasive rather than promotional. 3 emails, 3 problems. Email 1: Cardly.






















Let's personalize your content