Protecting Small Business Systems from Ransomware: Interview
ATAK Interactive
JUNE 9, 2017
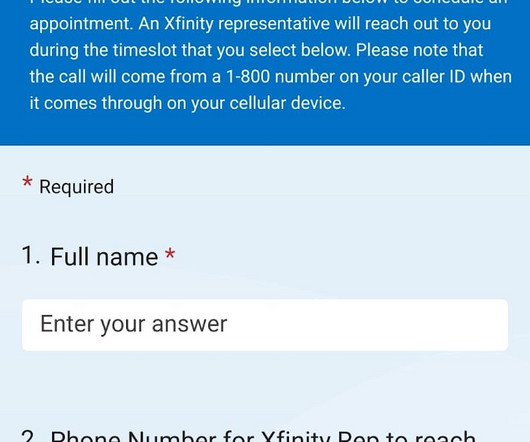
Usually, these are machines running Windows – since it’s the most popular operating system, and many users don’t keep their computer security and operating systems up to date, making that computer the most likely candidate to be subjected to a phishing attack. Fake URLs in an email. Misleading URLs in an email. Fake login pages.








































Let's personalize your content